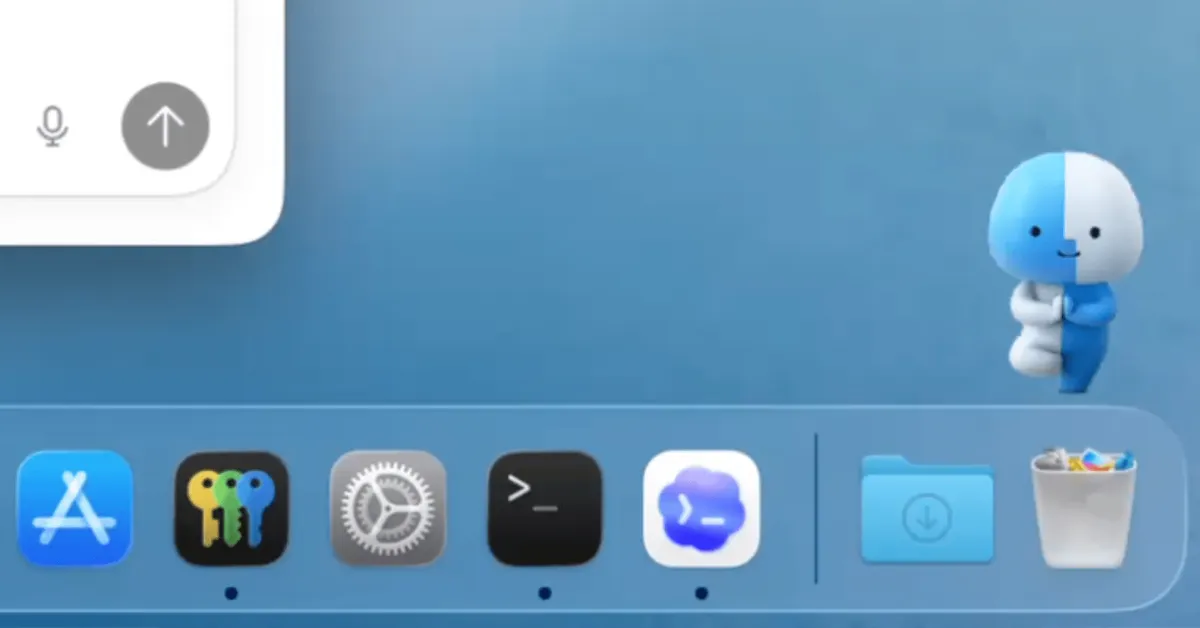
Apple has introduced a new security feature in macOS Tahoe 26.4 that detects potentially dangerous commands pasted into Terminal. When such commands are identified, the system halts execution and displays a warning to the user before proceeding. This change was not mentioned in Apple’s official release notes for macOS Tahoe 26.4, and users first noticed it after the release candidate build was made available.
The security measure appears to target ClickFix attacks, where users are tricked into pasting malicious commands into Terminal, often under the pretext of fixing a problem or verifying something. Since users must manually paste the commands, standard security protections are often bypassed.
How the macOS Tahoe 26.4 Terminal Paste Warning Works
When a user copies a command from Safari and pastes it into Terminal, the system delays execution and shows a warning. The warning informs users that the command has not yet been executed and warns that scammers typically distribute malicious instructions through websites and other channels.
Users have two options: they can cancel the paste if they do not trust the source or are unsure about the command, or they can proceed with execution if they recognize the command and wish to run it. Apple recommends that users continue as long as they understand what the command will do.
According to user tests reported on Reddit, the warning appears only once per Terminal session. In one test, pasting known destructive commands used in malicious activities did not trigger additional warnings after the initial warning was dismissed. Another user noted that pasting harmless commands did not trigger the warning either; this suggests some form of command analysis is being performed, but Apple has not provided a clear explanation of how the detection works.
Scope and Limitations of the New Terminal Paste Protection
Apple has not published a support document explaining how the warning system works, creating uncertainty about what detection criteria it uses or which command patterns trigger the warnings. It is also unclear whether the cut applies to commands pasted from sources outside of Safari or if Terminal sessions initiated through automation or scripts are controlled in the same way.
Since the detection method has not been disclosed, users should not rely solely on the warning to protect against ClickFix attacks. Commands from untrustworthy websites, emails, or support chats should not be executed even if a warning appears. BleepingComputer reached out to Apple for clarification, but the company has not publicly responded to questions about this feature at this time.



























![iPhone 17e: Apple Finally Got the Affordable iPhone Right [Video]](/resimler/iphone-17e-apple-nihayet-uygun-fiyatli-iphoneu-dogru-yapti-video.jpg)











Comments
(9 Comments)