Hacking groups linked to Iran have increased their cyber activities following recent missile attacks by the US and Israel. They are conducting digital scans, espionage operations, and distributed denial-of-service (DDoS) attacks across the Middle East.
Researchers indicate that most of the verified activities so far have targeted Israel and Persian Gulf countries, but US organizations should also be prepared for potential attacks.
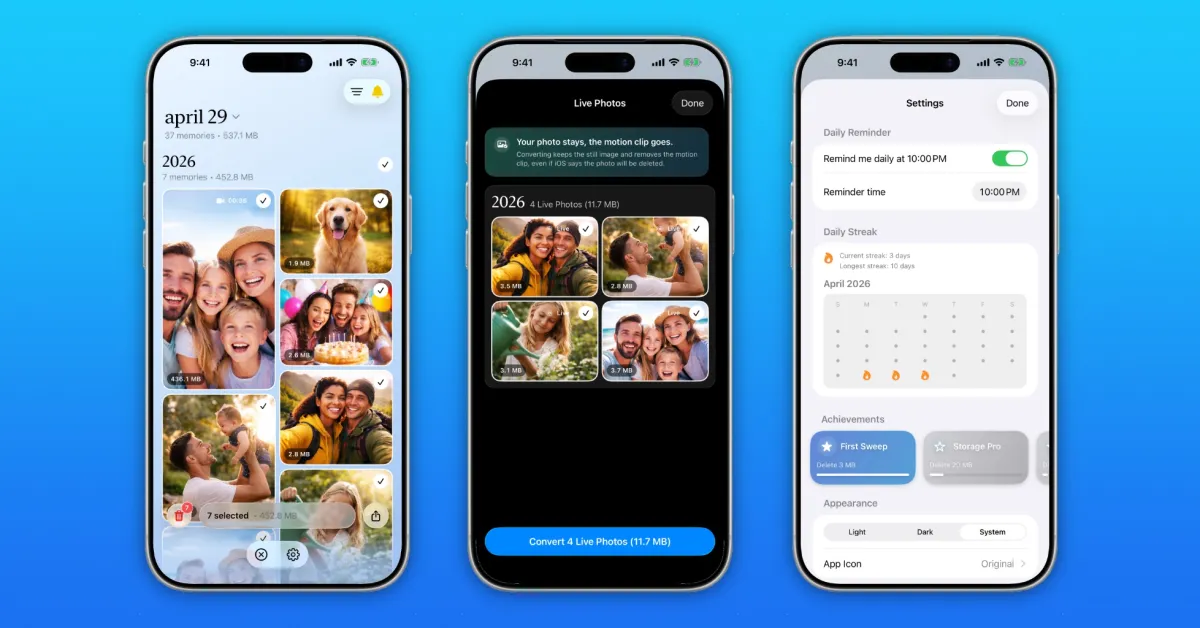
Iran Examines Mobile Applications and APIs Before Attacks
According to mobile application security firm Approov, Iranian hackers began conducting more advanced reconnaissance attacks in early February. These attacks focused on APIs and mobile applications used in government communications in the region.
These activities appear to have stopped on February 27. Experts believe this pause may be linked to the internet outage experienced within Iran at the onset of the conflict.
JP Castellanos, the threat intelligence director at Binary Defense, noted that Iranian groups have been placing malware on systems before an open military operation begins. This is a common tactic where attackers silently pre-position tools to launch more destructive attacks later.
Iranian Hackers Launched DDoS, Ransomware, and Misinformation Campaigns
Researchers at Check Point observed breaches linked to a group known as Cotton Sandstorm (also referred to as Haywire Kitten). This group is believed to be associated with the Islamic Revolutionary Guard Corps (IRGC).
According to the report, this group used a credential-stealing tool called WezRat in phishing emails that appeared to be urgent software updates. In some cases, ransomware attacks against Israeli targets occurred following these campaigns.
Analysts also noted that previously online identities have resurfaced, claiming to have hacked industrial control systems in Israel, Jordan, Turkey, Poland, and Gulf countries. Experts say that many of these public claims are exaggerated or part of broader misinformation efforts.
“Historically, Iran has tried to enhance the psychological impact by mixing real breaches with exaggerated or fabricated claims,” says an analyst.
US Organizations Could Be the Next Target
So far, there has been no publicly confirmed attack against US organizations during this latest wave of activities. However, researchers believe such attacks are possible.
The sectors at highest risk include:
- Defense contractors and government suppliers
- Organizations doing business with or sharing infrastructure with Israel
- Critical infrastructure providers such as energy or water services
- Companies using Israeli-made industrial technology
In the past, Iranian hackers targeted water systems and other operational technologies in the US. They often used default passwords and proprietary malware. Although these previous attacks caused limited physical damage, they demonstrated that attackers could access sensitive systems.
A Long-Standing Iranian Cyber Campaign
Experts indicate that the current situation appears to be part of a long-term cyber campaign that blends espionage, disruption, ransomware-style attacks, and information warfare.
They expect an increase in misinformation on social media through bots. People should anticipate seeing more dramatic claims about sabotage and damage to infrastructure; most of these are likely to be untrue.
Security firms recommend that organizations take the following actions:
- Quickly update critical systems
- Review user access and remove unused or default accounts
- Closely monitor third-party and supply chain risks
- Enhance phishing awareness training for employees
Researchers generally agree that cyber operations will continue alongside physical conflict. They warn that organizations in the US, Israel, and Gulf countries need to assess the risk urgently, not theoretically, but realistically.


































Comments
(2 Comments)